Achieving Cyber Essentials Certification: Understanding the Principle of Least Privilege
- The Assessor Team
- Feb 20
- 4 min read
Updated: Mar 2
If your organisation is preparing for a Cyber Essentials Certificate, one of the most important controls to understand is the principle of least privilege.
Many businesses focus heavily on firewalls, anti-malware, and patching. However, access control—specifically how user accounts are configured—is just as critical when considering how to get Cyber Essentials certified.
Under the Cyber Essentials scheme, organisations must ensure that user accounts are properly managed. Access to data and systems must be restricted appropriately. Least privilege is central to meeting this requirement.
What Is the Principle of Least Privilege?
The principle of least privilege (PoLP) means:
Users are granted only the minimum level of access necessary to perform their job role—no more, no less.
This principle applies to:
Standard user accounts
Administrative accounts
Cloud platform access
Shared drives
Third-party and contractor access
If you want to understand how to get Cyber Essentials certified successfully, implementing least privilege is a non-negotiable step.
Why Least Privilege Matters for a Cyber Essentials Certificate
Excessive permissions are one of the most common weaknesses identified during Cyber Essentials preparation.
If a compromised account has unnecessary access:
Attackers can move laterally across systems.
Sensitive HR or financial data can be exposed.
Ransomware impact increases.
The organisation’s ability to achieve a Cyber Essentials Certificate may be affected.
By limiting permissions, you:
Reduce breach impact.
Protect confidential data.
Align directly with Cyber Essentials access control requirements.
Strengthen your certification position.
Least privilege is not just best practice—it is practical risk reduction.
Practical Examples: Role-Based Access in Action
When organisations ask how to get Cyber Essentials certified, we often start by reviewing who can access what. Here are common examples.
Reception Staff
A receptionist typically requires access to:
Email
Calendars
Visitor management systems
Telephony systems
They do not require access to:
The CEO’s HR records
Employee medical information
Payroll systems
Confidential board documentation
Granting broad file-share access “for convenience” directly contradicts least privilege—and creates unnecessary risk.
Cleaning or Facilities Contractors
A cleaner may require:
Physical building access
Possibly a time-recording account
They do not require access to:
Accounts software
Sales ledger systems
CRM platforms
Financial reporting data
Even if risk appears low, unnecessary access increases exposure and weakens your Cyber Essentials posture.
Finance Team Members
A finance administrator may require access to:
Accounting software
Payroll platforms
Bank reconciliation systems
They generally do not require:
IT administrator rights
Server configuration permissions
HR disciplinary case records (unless role-specific)
Access should always align precisely with job responsibilities.
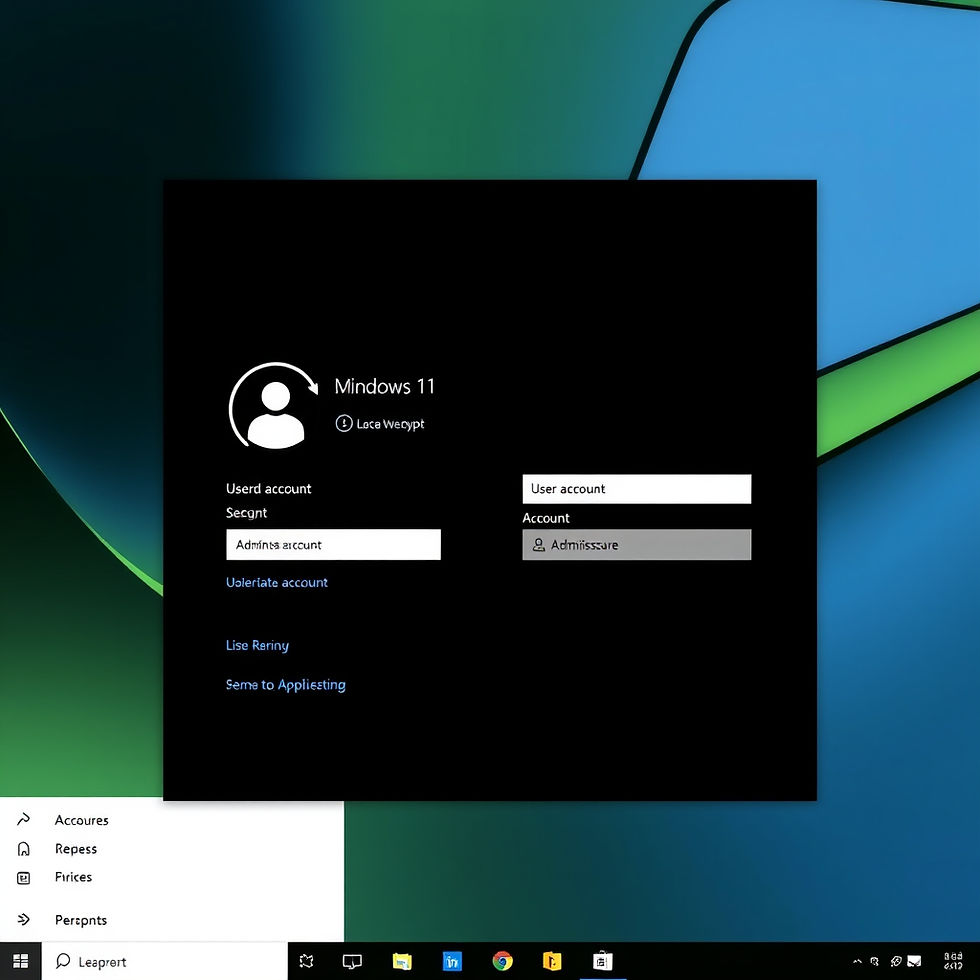
Administrative Privileges: A Critical Cyber Essentials Requirement
When working toward a Cyber Essentials Certificate, administrative privileges are a frequent point of failure.
Cyber Essentials requires that:
Admin accounts are limited to those who genuinely need them.
Administrative accounts are separate from standard user accounts.
Admin privileges are not used for everyday tasks like email or web browsing.
A common issue we see when organisations are learning how to get Cyber Essentials certified is multiple users having local administrator rights “because it’s easier.” This significantly increases the impact of phishing attacks or malware infections. Restricting admin rights is one of the fastest ways to strengthen your compliance position.
Implementing Role-Based Access Control (RBAC)
To meet Cyber Essentials requirements effectively, implement structured Role-Based Access Control:
Define clear job roles.
Map required system access to each role.
Remove default broad permissions.
Review access when staff change roles.
Immediately disable accounts when staff leave.
Without this structure, organisations often experience “permission creep,” where users accumulate access over time but never lose it.
Regular Access Reviews Support Certification Success
Least privilege is not a one-time configuration task. If you want to secure your Cyber Essentials Certificate, you should:
Conduct periodic access reviews.
Remove dormant or unused accounts.
Audit shared mailbox permissions.
Validate cloud access rights (e.g. Microsoft 365 or Google Workspace environments).
Access control must be demonstrably managed, not assumed.
Third-Party and Temporary Access Controls
External IT providers, consultants, and temporary staff must also follow least privilege principles. Access should be:
Limited to defined systems.
Time-bound.
Removed immediately when no longer required.
Monitored where appropriate.
Uncontrolled third-party access is a common weakness in organisations preparing for Cyber Essentials certification.
Common Access Control Mistakes Preventing Certification
When organisations struggle with how to get Cyber Essentials certified, we frequently identify:
Shared user accounts.
All-staff access to sensitive shared drives.
Excessive local administrator rights.
No documented access review process.
Active accounts for former employees.
Each of these can undermine your ability to obtain a Cyber Essentials Certificate.
Final Thoughts: Least Privilege Is Foundational
If you are serious about understanding how to get Cyber Essentials certified, start with user account permissions. Least privilege:
Reduces your attack surface.
Limits breach impact.
Protects sensitive HR and financial data.
Strengthens your compliance evidence.
Makes achieving your Cyber Essentials Certificate significantly more predictable.
Cyber security does not require complexity—it requires discipline. Give users exactly the access they need to do their job. Remove access they do not need. Nothing more. Nothing less.
Additional Considerations for Cyber Essentials Certification
Understanding Cyber Essentials Requirements
Before diving deeper into the specifics of least privilege, it’s essential to grasp the overall Cyber Essentials requirements. This certification is designed to help organisations protect themselves against common cyber threats. It provides a clear framework for managing security risks effectively.
The Role of Training and Awareness
Training staff on the importance of least privilege is crucial. Ensure they understand why access controls matter. Regular training sessions can help reinforce the principles of cybersecurity and the significance of adhering to access control policies.
Monitoring and Reporting
Implementing monitoring tools can help track access and identify potential breaches. Regular reporting can provide insights into user activity, ensuring compliance with least privilege policies. This proactive approach can help mitigate risks before they escalate.
The Future of Cyber Security
As cyber threats evolve, so must your security measures. Staying informed about the latest trends and technologies in cybersecurity is vital. Regularly updating your policies and practices will help maintain compliance with Cyber Essentials and protect your organisation from emerging threats.
Conclusion
Achieving Cyber Essentials certification is a journey that requires commitment and diligence. By understanding and implementing the principle of least privilege, you are taking a significant step toward enhancing your organisation's security posture. Remember, the goal is to protect sensitive data and reduce risks. Stay focused, stay informed, and keep your organisation secure!


Comments